Key Takeaways
How leading banks scale API governance without slowing innovation:
- Reduce Risk: Centralize IAM at the gateway to enforce least-privilege access
- Prioritize What Matters: Apply rate limiting after IAM to favor high-value partner traffic
- Enable Real-Time Compliance: Replace manual approvals with machine-readable policies
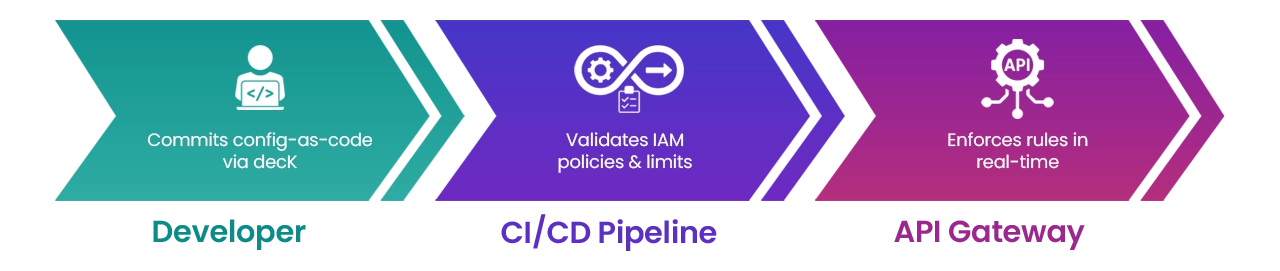
- Ensure Consistency at Scale: Use CI/CD and config-as-code to keep environments aligned
Maintaining systemic integrity and ensuring audit compliance are no longer peripheral technical concerns but have become foundational requirements for institutional stability and regulatory standing. The modern banking environment demands a transition from viewing APIs as short-project deliverables to treating them as long-term products governed by rigorous, machine-readable standards and centralized identity frameworks.
Foundational Resilience: Centralized IAM
In managing operational data platforms and central API integration layers, the challenge is not just about connecting services, but also doing so without creating a compliance debt. Compliance today depends on proving that every system-to-service interaction is authenticated, authorized, and logged with full traceability.
Many banks focus on the perimeter but may overlook internal access control. This could lead to credential sprawl, where developers and services hold overly broad permissions or orphaned admin rights.
At Stratpoint, we advocate that centralized Identity and Access Management (IAM) should come first. Implementing this on the API gateway on day 1 offers an immediate reduction in operational risk by:

Streamlining the Joiner-Mover-Leaver process
When an employee or partners departs, access is revoked across every environment instantly, eliminating the risk of ghost accounts.

Implementing traceability
Every request should be traceable to simplify audits and ensure you can evolve access controls seamlessly.

Enforcing least-privilege by default
Every service, API, and automation gets its own unique identity with scoped permissions.

Reducing cost
Centralization removes the need for fragmented, custom-built security logic within every microservice.
Smart Sequencing: Rate Limiting After IAM
Many teams attempt to protect their infrastructure by applying global rate limits at the gateway. However, without an identity context in place, you cannot distinguish between a routine internal service and high-priority traffic from a partner ecosystem, a distinction vital for open banking readiness. Rate limits without IAM are blind. You are capping traffic without knowing who is consuming it.
By layering rate limiting on top of IAM, you gain the ability to enforce limits based on:
- Specific roles or systems: Prioritize high-value revenue streams and critical partner integrations over low-priority internal tasks.
- Environment context: Adjust limits dynamically based on whether the traffic originates from a trusted partner or a new integration.
Start with IAM to create structure, then layer rate limiting on top to manage traffic intelligently and ensure the platform is built for the scale and fairness required by an open financial ecosystem.
Policy-Driven Control: Speed Meets Compliance
Automation at the Gateway